Abolished for six years in the United States, net neutrality finally marks its return: the American Telecommunications Authority decided on...
(Montreal) Bombardier reported lower profits and revenue in the first quarter, but said its order backlog grew compared with the...
Host Paul LaRocque raised his glass to the quality of the discussion among the panelists on the show The Joust...
This page will probably be the last in my notebook. As a secondary school teacher, I had the enormous privilege...
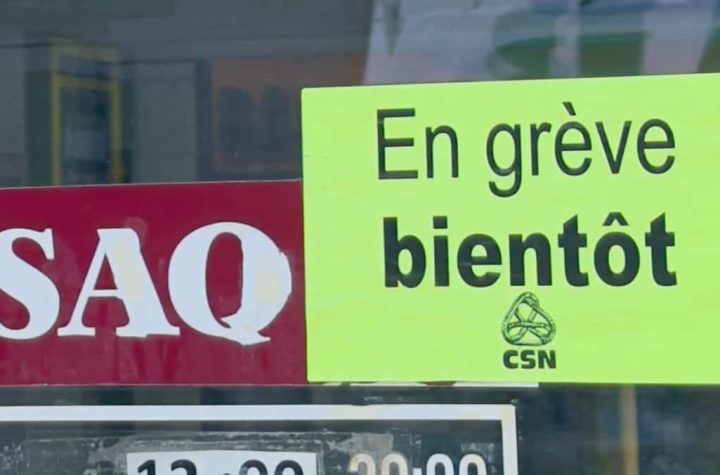
The store and office workers union of the Société des Alcohols du Québec, which represents about 5,000 workers in the...
The number of service disruptions on Réseau Express Métropolitan has increased with the arrival of colder weather, according to new...
All indications are that the Société des alcools du Québec (SAQ) will have to operate without employees on Wednesdays and...
For many people, eating a glass of milk, grain products, or certain fruits and vegetables can cause food intolerances such...
Several mayors from the metropolitan area called on the provincial government on Monday to take advantage of a new provision...
Ten Desjardins service centers will close their doors in Bas-Saint-Laurent in two months, TVA Nouvelles has learned that a significant...